La herramienta solo sirve para la vulnerabilidad del Intel Engine Management (IME).
La herramienta corresponde para la vulnerabilidad que salio a la luz el año pasado, no para las vulnerabilidades de este año, Meltdown y Spectre.
.Intel® Management Engine Critical Firmware Update (Intel-SA-00086)
Last Reviewed: 26-Dec-2017
Article ID: 000025619
Intel® Management Engine (Intel® ME 6.x/7.x/8.x/9.x/10.x/11.x), Intel® Trusted Execution Engine (Intel® TXE 3.0), and Intel® Server Platform Services (Intel® SPS 4.0) vulnerability (Intel-SA-00086)
In response to issues identified by external researchers, Intel has performed an in-depth comprehensive security review of the following with the objective of enhancing firmware resilience:
Intel® Management Engine (Intel® ME)
Intel® Trusted Execution Engine (Intel® TXE)
Intel® Server Platform Services (SPS)
Intel has identified security vulnerabilities that could potentially impact certain PCs, servers, and IoT platforms.
Systems using Intel ME Firmware versions 6.x-11.x, servers using SPS Firmware version 4.0, and systems using TXE version 3.0 are impacted. You may find these firmware versions on certain processors from the:
1st, 2nd, 3rd, 4th, 5th, 6th, 7th, and 8th generation Intel® Core™ Processor Families
Intel® Xeon® Processor E3-1200 v5 and v6 Product Family
Intel® Xeon® Processor Scalable Family
Intel® Xeon® Processor W Family
Intel Atom® C3000 Processor Family
Apollo Lake Intel Atom® Processor E3900 series
Apollo Lake Intel® Pentium® Processors
Intel® Pentium® Processor G Series
Intel® Celeron® G, N, and J series Processors
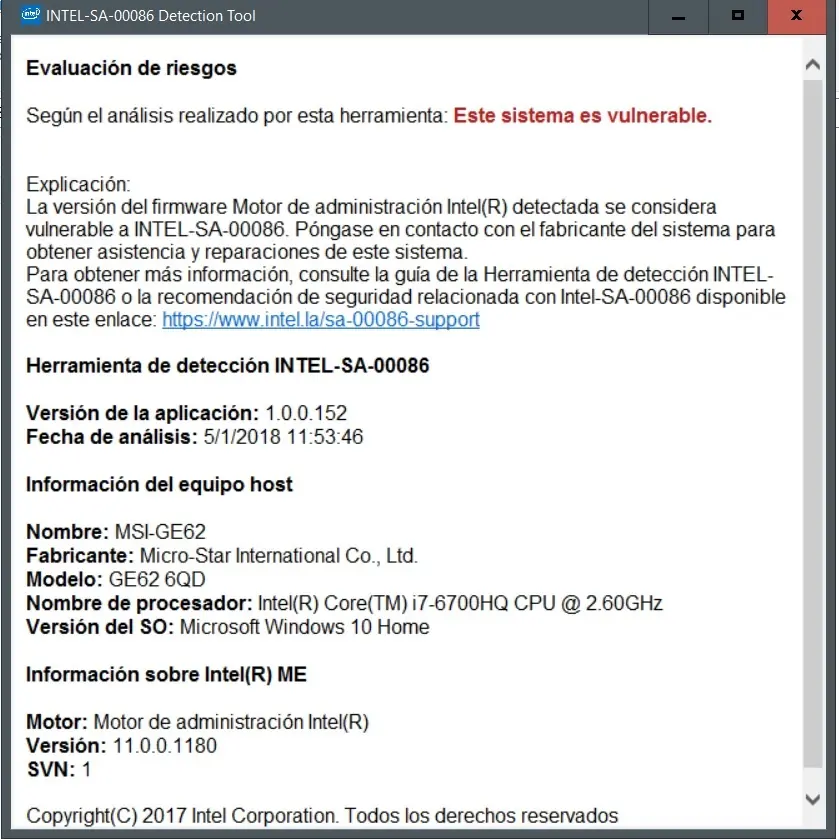
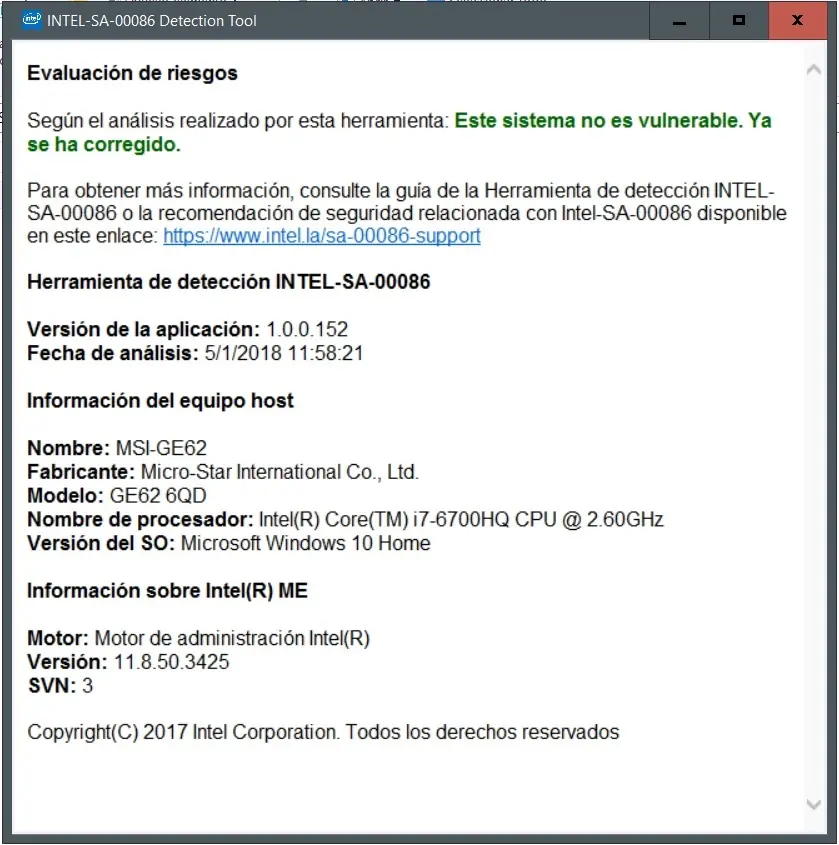
To determine if the identified vulnerabilities impact your system, download and run the Intel-SA-00086 Detection tool using the links below
En mi caso, MSI largo actualizaciones para el BIOS de mi notebook.
Resumen LVL 5: La herramienta de intel no sirve para Meltdown y Spectre, solo para una vulnerabilidad en Intel ME. Todos somos vulnerables, al menos que actualizes el bios.